Brand safety is now a CMO + CISO problem.
Why the next budget line item belongs to neither team alone — and how to structure the conversation.
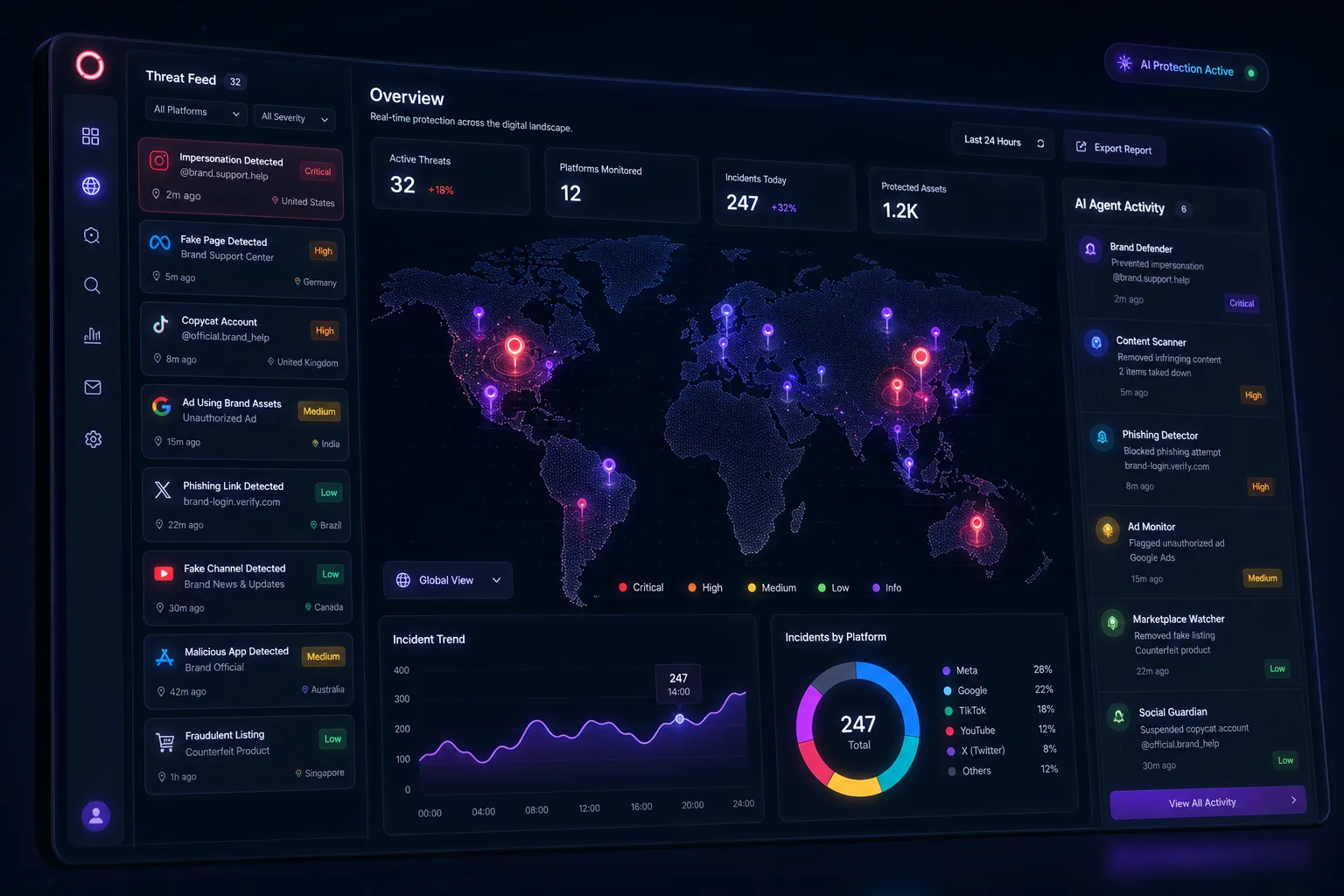
Read article →Tactive is the AI agent that defends your brand across the ad ecosystem — 24/7, autonomously. It detects deepfakes, fake storefronts, and impersonation attacks before they reach your customers.
AI didn't just speed up fraud — it weaponized creativity. Attackers can now clone your voice, your visual style, and your tone using nothing but public content. There is no dominant tool to defend against it. Until now.
A new attack is attempted every five minutes. Most never reach the security team — they hit your customers first.
Pindrop reports nearly a third of all fraud attempts now use generative AI to bypass detection.
Chainalysis found AI-enabled scams generate 4.5x more revenue per operation than traditional ones.
iProov 2024. Yet only 13% of companies have any anti-deepfake protocol in place. The gap is the opportunity.
Vibe-jacking — attackers cloning a brand's voice, visual style, and tone using public content — is now a named category of attack. There is no dominant tool to defend against it.
Connect Tactive to your ad accounts, brand assets, and websites. The agent runs continuously across Meta, Google, TikTok, YouTube, search results, and the open web — detecting, deciding, and acting on its own.
Monitors ad platforms, search results, app stores, social, and the open web for unauthorized brand use, deepfakes, fake storefronts, and impersonation.
An AI classifier scores every signal by severity and likely intent — separating noise from a brand-damaging incident in real time.
Files takedowns, alerts your team, and at higher tiers auto-pauses compromised campaigns or auto-submits platform reports.
Tactive is one product, not three. You activate the modes that match your biggest risks — and add more as you grow.
Stops impersonation before it reaches customers.
Catches the silent failures that bleed budget.
See competitor moves the moment they ship.
Tactive replaces the dashboard with a feed: prioritized incidents, suggested actions, and a one-click trail of everything the agent has already handled while you slept.
Each tier is a step up in autonomy: Watch → Defend → Command. Start where you are. Graduate when you're ready.
Entry — solo operators & small brands
"Deepfake-era brand monitoring no one else gives small brands."
Growth — marketing teams at scaling brands
"Full agent, full coverage, predictable price."
Enterprise — agencies & large brands
"Replaces 2–3 vendors. Sits inside the security stack."
All tiers include continuous monitoring · No setup fees · Cancel anytime
The capabilities Tactive already has — ad monitoring, brand surveillance, alerting — are now demanded by a buyer who didn't exist two years ago. No new tech needed; just a reframe.
Enterprise brand-protection tools (ZeroFox, BrandShield, Memcyco) start in the five-figure range. Marketing tools that do brand monitoring as a side feature don't take it seriously. Tactive owns the mid-market gap — credible defense for brands too small for enterprise security but too valuable to ignore impersonation.
In 2026, every category is being reframed around AI agents. Tactive can credibly do this without a rebuild because the platform already does autonomous monitoring — it just hasn't been called that.
Field reports, frameworks, and intelligence on the new threat surface — published monthly.

Why the next budget line item belongs to neither team alone — and how to structure the conversation.
Read article →
Five-stage anatomy of a modern impersonation attack — and the response model that stops it.
Read article →
Attackers no longer need your assets — they need your aesthetic. Here's how to recognize and respond to it.
Read article →